Can IoT (Internet of Things) harm my compliance and open my business to attack?
Review this short 3-min video which describes an IoT attack method
What is IoT? IoT (Internet of Things) is one of the fastest-growing areas of hardware deployment in business today. IoT devices include connected thermostats (such as NEST), door controllers, sensors, robotics, lighting controllers and many many other time- and money-saving devices. Basically these are devices which are intended to be attached easily to a network and which are typically connected to the cloud.
IoT is easy to buy
IoT is easy to deploy
IoT is easy to manage
What's not to love? Statistics say that over 40% of residences worldwide have at least one IoT device. In North America over 60% of homes have an IoT device. Over 20 billion IoT devices will be deployed by 2020.
IoT is almost never secured out-of-the box
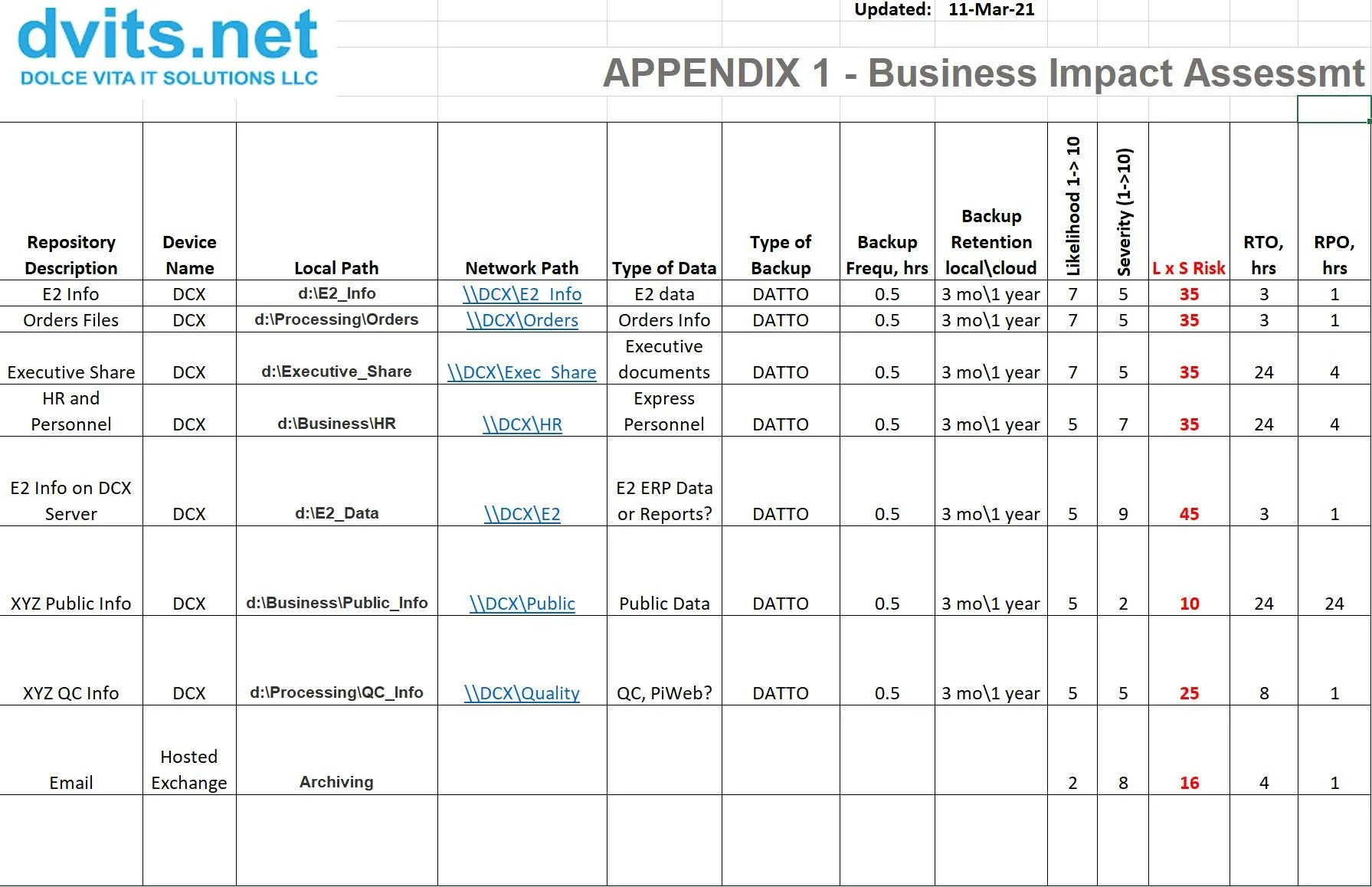
IoT can easily damage your IT compliance
Think about the most recent IoT device you installed. It gave a one-page instruction sheet which was 4-7 lines in length:
this is what’s in the box
this is how you power it up
this is the information you need to connect it to your wireless network
this is how you log into the controller or the device
this is how you verify that it works
Easy, right? Think about it again.
When you powered it up, did you connect it to your business network (with all your finance and other sensitive data)? Why?
When you configured it, did you verify that it has the latest authenticated firmware version?
When you configured it, did you set strong complex credentials (more than 8 characters using upper case, lower case, numbers, and special characters)? Does the device even support such a credential?
When you configured the management console in the cloud, did you configure it to use strong, complex credentials?
Default credentials for these devices are published…hopefully your device came out of the box with a unique password, but well over 90% do not.
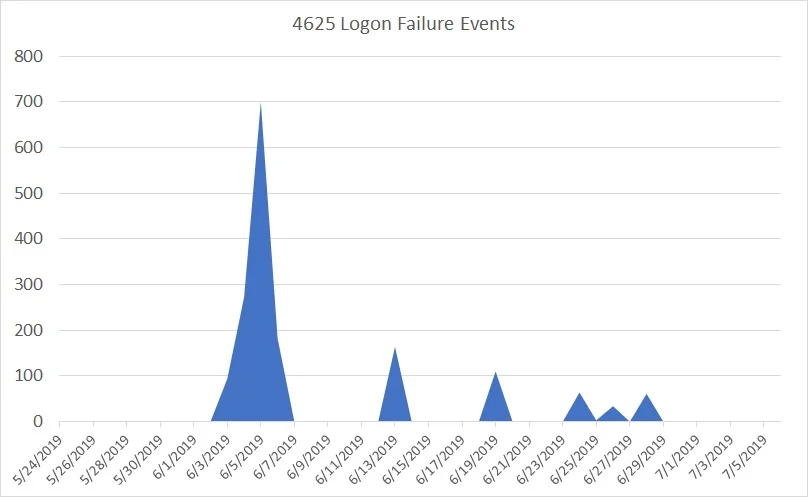
IoT devices rarely support policies…so an attacker has unlimited tries to penetrate the credentials in use. It will never lock them out!
IoT devices rarely support logging, so how would you even know if an attack were being attempted?
IoT devices can be used as a jumping-off point for an attacker to access, compromise or collect data from your network.
Be smart!
is the IoT device essential to your business?
Put the device on a guest network (internet access only) or a dedicated network separate from your business network.
Verify that the device is using the most secure firmware version tested by the manufacturer…if they do not offer firmware updates, you know they are not considering security.
Set strong, complex credentials both on the device and any management console.
If the device supports policies such as lock-out then have it lock out after 5-10 bad credential attempts for 20-60 minutes. If the controller can provide logging, ensure it is enabled.
Be sure that you know of ANY IoT device used on your business network, and verify that they are secured properly.
If it is an mission-critical IoT system (robotics, manufacturing systems, etc.) the controller should support multi-factor authentication. Enable it and use it!
Get our IoT whitepaper now to find out how to better protect your business!