How can "spring cleaning" reduce your business risks?
Of course Spring is a natural time to reset and re-evaluate…and that idea applies every bit as much to your business data as it does to your office (and your home). While most organizations focus on cleaning physical spaces, “spring cleaning” your data can significantly reduce business risk and strengthen your cybersecurity posture.
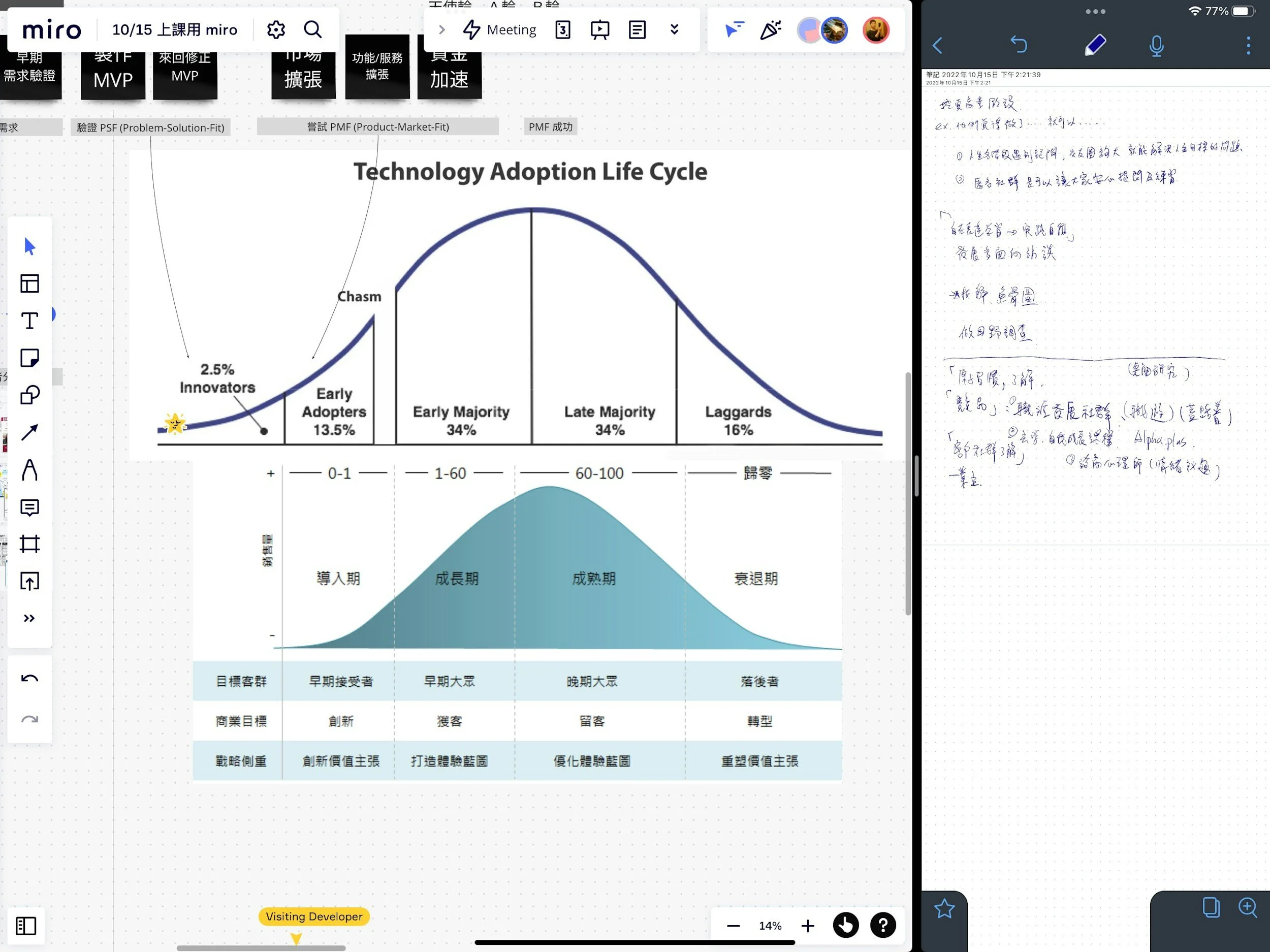
Over time, companies accumulate large amounts of outdated, duplicate, or unnecessary data. This includes old customer records, former employee records, unused and obsolete (read that as unsafe) applications, and forgotten file shares. Each of these represents potential exposure. If sensitive data is stored longer than necessary or in unsecured locations, it increases the risk of breaches and compliance violations.
A structured data clean-up helps reduce that exposure. Start from your latest business impact assessment…you remember, the policy item where you document your business data repositories. It spells out what data you have, where it resides, and how it is backed up. Use that list to prioritize how you CAREFULLY plan the data which can be destroyed or possibly archived. Remove or archive anything that no longer serves a business purpose—especially sensitive information like protected health information (PHI), financial records, or intellectual property that is no longer actively used.
Access control is another key component. During your clean-up, review user permissions and eliminate access for former employees, vendors, or users who no longer need it. Limiting access reduces the likelihood of insider threats and credential-based attacks. Use your vulnerability scans to identify and remove stale user and computer accounts. If you use Microsoft 365 and always thought it might be a good idea to implement better data governance policies to flush old data…why not now?
Ideally these cleanups are done on a regular basis…but unsurprisingly with as busy as every business is, its easy to put this off. The result over time is more organization friction with time wasted just trying to locate specific data, or track down last year’s audit responses, or finding that part of the business plan you were working on just last month!
You should also evaluate your backup and retention policies. Keeping excessive backups or retaining data indefinitely may seem safe, but it can increase risk if those backups are compromised. Align technical retention policies with your written policies and compliance requirements.
Finally, take the opportunity to better standardize and secure your environment. Consolidate data into approved systems, enforce encryption and multi-factor authentication where appropriate, and ensure monitoring tools are in place.
A thoughtful data “spring cleaning” doesn’t just improve organization—it actively reduces your attack surface, simplifies compliance, and strengthens your overall cybersecurity resilience. For many businesses, it’s one of the most practical and cost-effective risk reduction steps they can take.